LulzSec Hacks
Added 12 years ago by Don • Updated about a year ago by Don
| Navigation |
| Overview • Background • Notable Developments • Trial • Search Interest • External References • |
Type: Hack
Tags: hacking sony 4chan lulz activism ddos hack events of 2011 protest nyan hacker
Additional References: Wikipedia
Overview
Lulzsec Hacks refers to a series of high profile cyber-attacks carried out by the computer hacking group Lulzsec (Lulz Security) beginning in May 2011. Some of the most notable targeted websites include Sony Pictures' internal database, CIA website and FBI's contractor InfraGard among others. Although the group officially announced its retirement in June 2011 and suspect members of Lulzsec have been taken into police custody, numerous related attacks have been reported by its affiliated groups since then.
Background
The group periodically releases stolen information from websites. They post the stolen data on their website in .txt files[9], on the web app pastebin or in torrents on their page on The Pirate Bay[10]. Releases often are posted on Fridays and thus they made a hash tag called “#fuckfbifriday” that they use to tweet with. They have been known to use Distributed Denial of Service (DDOS) attacks and SQL injections to take down websites. The group appears to be mainly motivated by political causes related to economic and social justice, but also seem to appreciate hacking for pure entertainment. (See also: #OpSony)
Notable Developments
The group periodically releases stolen information from websites. They post the stolen data on their website in .txt files[9], on the web app pastebin or in torrents on their page on The Pirate Bay[10]. Releases often are posted on Fridays and thus they made a hash tag called "#fuckfbifriday" that they use to tweet with.
May 5th, 2011: FOX
The earliest known hack attributed to the group began on May 5th, 2011 against Fox Broadcasting Company, which resulted in the breach of TV talent show X Factor contestants database and 73,000 applicants' personal information. On May 10th, Fox.com sales database and users' personal information was released.
We're releasing the X-Factor contestants database publicly tonight. Stay tuned. Wink, wink, double wink!
— The Lulz Boat (@LulzSec) May 6, 2011
May 27th – June 6th: SONY
Between late May and early June 2011, international media company Sony's database was attacked by hackers who took thousands of users' personal data including "names, passworsd, e-mail addresses, home addresses dates of birth." Lulzsec claimed that it used a SQL injection attack and was motivated by Sony's legal action against the original iPhone jailbreak hacker George Hotz, who revealed similar information of Sony's PlayStation 3 console in December 2010.
Hey guys, we took a cruise! Who wants to play spot the SonyMusic SQLi? #fun #fun #FUN
— The Lulz Boat (@LulzSec) May 24, 2011
The breached databases include Sony Music Japan, Sony Pictures, SonyBMG Netherlands and SonyBMG Belgium. The group claimed to have compromised over 1,000,000 accounts, though Sony claims the real figure was around 37,500. Some of the compromised information has been reportedly used in scams.
May 29th: PBS
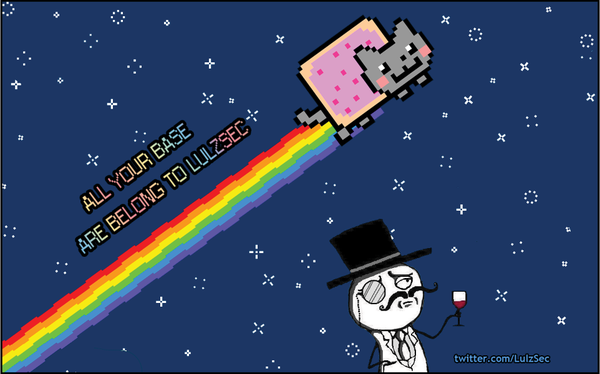
On May 29th, 2011, LulzSec managed to compromise several PBS web properties including their official website and Twitter account. The PBS homepage was defaced with an image of Nyan Cat and the words "all your base are belong to lulzsec" referecing All Your Base Are Belong To Us. They claimed it was in response to a biased documentary about Wikileaks that had aired on an episode of PBS Frontline. They also were responsible for an article which claimed that 2Pac, a rapper who died back in 1996[7], was still alive and was found living in New Zealand with another famous dead rapper, Biggie Smalls[8].

June 15th: CIA
LulzSec took responsibility for taking down the United States Central Intelligence Agency website in a tweet[1] on June 15th, 2010. According to Gawker reporter Adrian Chen[2], the attack was meant to impress Twitter user Quadrapocdacone:
This afternoon, Quadrapodacone and Lulzsec got into a Twitter flame war, after Quadrapodacone mocked Lulzsec for taking on only "soft targets" like video game companies and PBS. (Lulzsec has since deleted its side of the conversation.)
Tango down – cia.gov – for the lulz.
— The Lulz Boat (@LulzSec) June 15, 2011
June 15th: War With 4chan
An article was posted to the website VentureBeat claiming that LulzSec was starting to attack users of the website 4chan.org, and the nebulous group referred to as "Anonymous", on June 15th, 2011.
The sparring began when LulzSec initiated a “DDoS Party,” which was a set of large-scale distributed denial of service attacks on several gaming servers and websites that brought a lot of games offline. EVE Online, League of Legends and Minecraft all faced outages or significant latency problems. That was enough to get the attention of “/v/,” an internal image sharing board on 4chan.org that focuses on video games.[3]
June 17th: SEGA Attack Denial
On June 17th, 2011, multinational videogame developer company SEGA issued an e-mail to its online network SEGA Pass subscribers revealing that the network was breached by a group of hackers and an unknown number of subscribers' personal information were stolen, such as e-mails and date of birth:
"Over the last 24 hours we have identified that unauthorised entry was gained to our Sega Pass database," the company said. "We immediately took the appropriate action to protect our consumers' data and isolate the location of the breach. We have launched an investigation into the extent of the breach of our public systems."
On the next day, Lulzsec responded to the news on Twitter by denying an involvement with the attack on Sega Pass. In a tweet expressing their fancy for the aging console Dreamcast, @Lulzsec announced that they will help the company to take down whoever launched this attack in retaliation:
— The Lulz Boat (LulzSec) June 17, 2011
Sega - contact us. We want to help you destroy the hackers that attacked you. We love the Dreamcast, these people are going down.
June 17th: War With Anonymous Denial
On June 17th, 2011, the @LulzSec Twitter account announced that they are not at war with Anonymous, and repeated the sentiment by retweeting @YourAnonNews:
Saying we're attacking Anonymous because we taunted /b/ is like saying we're going to war with America because we stomped on a cheeseburger.
— The Lulz Boat (@LulzSec) June 17, 2011
We are NOT at war with
— Anonymous (YourAnonNews) June 17, 2011LulzSec #MediaFags
June 19th: Operation Anti-Security (#AntiSec)
On June 19th, 2011, LulzSec posted a statement on pastebin[5] announcing that they will be teaming up Anonymous to attack government agencies.
Welcome to Operation Anti-Security (#AntiSec) – we encourage any vessel, large or small, to open fire on any government or agency that crosses their path. We fully endorse the flaunting of the word "AntiSec" on any government website defacement or physical graffiti art. We encourage you to spread the word of AntiSec far and wide, for it will be remembered. To increase efforts, we are now teaming up with the Anonymous collective and all affiliated battleships.
June 20th: SOCA
On June 20th, 2011, LulzSec managed to take down the United Kingdom's Serious Organized Crime Agency (SOCA) website with a DDoS attack as part of Operation Anti-Security.
Tango down – soca.gov.uk – in the name of #AntiSec
— The Lulz Boat (@LulzSec) June 20, 2011
June 21st: Brazilian Government Websites
On June 21st, a South American branch of Lulzsec group (@LulzSecBrazil) launched DDoS attacks against the portal of Brazilian government websites and the homepage of the President under the banner of Operation Anti-sec. The denial-of-service attacks came following the announcement on June 19th of a joint operation seeking to "steal and leak any classified government information, including email spools and documentation."
Since the beginning of Operation Anti-sec, LulzSec's support base has expanded from small unknown groups to an international network of Anonymous activists and regional Lulzsec chapters in Brazil and Colombia, as well as the Iranian Cyber Army.
June 23rd: Arizona Department of Public Safety
On June 23rd, Lulzsec also released a new set dubbed "Chinga La Migra," a Spanish phrase meaning "fuck the border patrol," which reveals hundreds of private intelligence bulletins, personal information of police officers and confidential documents including training manuals and personal email correspondence. In the press release, the group cited the legislation of SB1070 (Support Our Law Enforcement and Safe Neighborhoods Act), a controversial anti-immigration law that was passed in the state of Arizona in April 2011, as their primary motive behind targeting the Department of Public Safety.
The documents classified as "law enforcement sensitive", "not for public
distribution", and "for official use only" are primarily related to border
patrol and counter-terrorism operations and describe the use of informants to
infiltrate various gangs, cartels, motorcycle clubs, Nazi groups, and protest
movements.
Presenting Chinga La Migra: thepiratebay.org/torrent/649079… | lulzsecurity.com/releases/ching… #AntiSec
— The Lulz Boat (@LulzSec) June 23, 2011
June 25th: LulzSec Retires
On June 25th, 2011, LulzSec released a statement on pastebin[11] saying that after 50 days of hacking, they will be going into retirement.
50 Days of Lulz statement: pastebin.com/1znEGmHa | Torrent: thepiratebay.org/torrent/649552… Thank you, gentlemen. #LulzSec
— The Lulz Boat (@LulzSec) June 25, 2011
We are Lulz Security, and this is our final release, as today marks something meaningful to us. 50 days ago, we set sail with our humble ship on an uneasy and brutal ocean: the Internet. The hate machine, the love machine, the machine powered by many machines. We are all part of it, helping it grow, and helping it grow on us.
They later tweeted that Operation Anti-Security would be passed on completely to Anonymous:
Finally, we encourage all future #AntiSec enthusiasts to join the AnonOps IRC here: bit.ly/kXnGnn and follow
— The Lulz Boat (LulzSec) June 25, 2011AnonymousIRC for glory!
The farewell statements were also accompanied with about 458 MB of data from AOL, AT&T, Navy.mil, pilimited.com, and many other websites that they uploaded from their Pirate Bay account[10].
July 13th: LulzSec Announces a "Mystery Operation"
On July 13th, 2011, LulzSec announced that once @pastebin reched 75,000 users they would embark on a mystery operation that would "cause mayhem." After their announcement, @pastebin recived about 10k followers in 6 days.[12]
July 19th: LulzSec Hacks The Sun
On July 18th, the retired hacker group resumed its activities when they reportedly hacked the homepage of News International-owned The Sun to display a fake story about NewsCorp's CEO Rupert Murdoch's death from a drug overdose:

Media moguls body discovered
Rupert Murdoch, the controversial media mogul, has reportedly been found dead in his garden, police announce. Murdoch, aged 80, has said to have ingested a large quantity of palladium before stumbling into his famous topiary garden late last night, passing out in the early hours of the morning.
“We found the chemicals sitting beside a kitchen table, recently cooked,” one officer states. “From what we can gather, Murdoch melted and consumed large quantities of it before exiting into his garden.”
Authorities would not comment on whether this was a planned suicide, though the general consensus among locals and unnamed sources is that this is the case.
One detective elaborates. “Officers on the scene report a broken glass, a box of vintage wine, and what seems to be a family album strewn across the floor, containing images from days gone by; some containing handpainted portraits of Murdoch in his early days, donning a top hat and monocle.”
Another officer reveals that Murdoch was found slumped over a particularly large garden hedge fashioned into a galloping horse. “His favourite”, a butler, Davidson, reports.
Butler Davidson has since been taken into custody for additional questioning.
As the volume of requests exploded on the news site, the group then redirected its homepage to their Twitter account[13]. LulzSec also confirmed its responsibility for the hack and released a number of e-mails and passwords presumably associated with The Sun employees via Twitter. The tech blog Gizmodo[14] also reported that one of the passwords tweeted out by "Anonymousabu" belongs to the recently arrested News International chief Rebekah Brooks:
TheSun.co.uk now redirects to our twitter feed. Hello, everyone that wanted to visit The Sun! How is your day? Good? Good!
— The Lulz Boat (@LulzSec) July 18, 2011
If you visited The Sun before we did this (may God have mercy on your soul) clear your cache so the redirect works. #MurdochMeltdownMonday
— The Lulz Boat (@LulzSec) July 18, 2011
September 23rd: Proxy Information Leak
The FBI was able to find Kretsinger through activity logs they obtained from the UK proxy service Hide My Ass.[24] In IRC chat logs published by the Guardian[28] in June 2011, Hide My Ass, or HMA, was referred to as the proxy they were using. On September 23rd, the day after the arrests, Hide My Ass published a blog post[25] stating that their "VPN service and VPN services in general are not designed to be used to commit illegal activity," condemning the actions that were supposedly performed by LulzSec using their services.
Several other VPN providers, including AirVPN[26], came out against Hide My Ass's actions. AirVPN specifically noted that their company does not keep logs of their users' actions and included instructions on how to use their services without providing any type of trail. Privacy International[27] pointed out that Hide My Ass was closely involved with helping Egyptians get access to Twitter and other government-blocked sites during the Arab Spring protests.
December 2011 Attacks
On December 3rd, 2011, the Examiner[30] reported that LulzSec had launched several DDoS attacks against the Bank of Portugal and a number of government sites in retaliation of police violence toward protesters during demonstrations on November 24th.
On Friday, LulzSec Portugal launched a DDoS attack against the website of Banco de Portugal (Bank of Portugal), making the site inaccessible. In addition to taking down the Bank of Portugal website, LulzSec Portugal has been credited with successful attacks on numerous state services. Earlier this week, LulzSec disabled the websites of the Portugal House of Parliament, several political parties, and the national police.
On December 12th, 2011, the Examiner[29] published an article revealing that a conservative Christian group, the Florida Family Association, was being attacked by members of both LulzSec and Anonymous.
On Monday, a hacktivist identified as ih@zcAnNONz and working under the flag of Anonymous and LulzSec issued a Pastebin release with email and IP addresses of Florida Family Association members receiving newsletters, as well as a sample of members credit card information offered as proof of the hack.
In addition, the official Florida Family Association official website went down due to a DDoS attack on December 12th.
Anonymous posted an explanation for the attacks into a Pastebin[32] on December 11th, which claimed the attacks were in retaliation for bigotry against various groups:
Florida Family Association…
Your hatred, bigotry and fear mongering towards Gays, Lesbians and most recently
Muslim Americans has not gone unnoticed!
Anonymous will not stand for hate and divisive vitriol to be spread across our country and whenever we can…we will stop it…
FFA you managed to use your power to influence Lowe's to follow you into your racist stupor and they too will answer for that…
For now, you will answer to it… as well as your unfortunate followers having personal information shared with the world so everyone can know how racist and hateful you all are.
I am going to assume most of the people who receive your newsletter, email you and make donations are potentially part of the 99%. They are likely lower middle class people who have been mislead by all of your bullshit and god talk…therefor they too are unwitting victims. So I will NOT share all of the Credit Card information I got.
I am though reading the emails and getting information on those who did donate to make sure they are not worthy of the scorn of Anonymous as well…if i find information such as anyone being a part of other hate groups such as the Klan or anything similar all bets are off for those people.
I want all of your followers to know though their information is NOT SAFE in your hands until you address your security issues.
I AM ALSO GOING THROUGH ALL OF YOUR EMAILS RIGHT NOW…YOU SEEM TO GET AS MUCH OR MORE HATE MAIL THAN GOOD MAIL…HOW DOES THAT MAKE YOU FEEL???
=======
WE ARE ANONYMOUS
WE ARE LEGION
WE DO NOT FORGIVE
WE DO NOT FORGET
YOU SHOULD HAVE EXPECTED US!!!
February 3rd: FBI and Scotland Yard Conference Call Leak
On February 3rd, 2012, a recording of an FBI conference call with Scotland Yard was uploaded to YouTube by TheDigitalfolklore.[33] The 17-minute call caught the law enforcement officers joking around with each other and discussing the court proceedings of members of LulzSec including Kayla.
The leak of this call, which took place on January 17th, 2012, was covered by BoingBoing[34], Talking Points Memo[35], the Guardian[36], and the BBC.[37] The same day the YouTube video was uploaded, the FBI confirmed that Anonymous members had obtained an email with the time, telephone number, and access code for the call[38] and had not hacked into any FBI facilities.
March 6th: Sabu Revealed as Snitch
On March 6th, 2012, five members of LulzSec were charged by the U.S. Department of Justice[39] with varying computer hacking offenses related to attacks on FOX, Sony, and PBS websites in 2011. The members arrested included Ryan Ackroyd (Kayla) and Jake Davis (Topiary) of England, Darren Martyn (Pwnsauce) and Donncha O'Cearrbhail (Palladium) of Ireland, and Jeremy Hammond (Anarchaos) of Chicago, Illinois.[53][54]
Additionally, Hector Xavier Monsegur, better known as Sabu[48], was revealed to have pled guilty to twelve counts[43] of hacking conspiracies on August 15th, 2011, having worked with the FBI shortly after his arrest in June 2011.[40] As part of his plea deal, Monsegur agreed to "actively cooperate with the government,"[41] providing federal agents with details on other suspects involved in similar cases. This information came less than 24 hours after an anti-government tweet was made on Sabu's official Twitter account.[61]
The federal government is run by a bunch of fucking cowards. Don't give in to these people. Fight back. Stay strong.
— The Real Sabu (@anonymouSabu) March 5, 2012
Sabu's cooperation with the FBI has been rumored on several occasions. On August 17th, 2011, Sabu disappeared from Twitter[42] after Gawker published a leaked chat log revealing his detailed knowledge regarding the arrest of Topiary. Later that month, another hacker known as Virus told Gizmodo[46] that he believed Sabu's disappearance meant he cut a deal with the FBI. That November, was once again rumored to be an informant[44][45], due to the servers he was using to access the Anonops IRC channel as well as the email he used to register his IRC nickname: compromise@gmail.com.
The news story was picked up by the Huffington Post[49], Reuters[50], TIME[51], Forbes[52], the Guardian[55], Fox News[56], the New York Times[57], CNN Money[58], the Wall Street Journal[59] and BBC News.[60] Amidst the news coverage, it was revealed that Sabu was arrested by the New York Police Department on February 3rd, 2012 for posing as a federal agent[47] and charged with second degree criminal impersonation.
March 17th: Lulzsec Announces Return
Over a week after the FBI arrests of five additional Lulzsec-related suspects, YouTube channel FawkesSecurity posted a video titled "LulzSec Returns," claiming the anti-government hacking movement will resume on April 1st, 2012 with attacks against various government and corporate agencies.
“Much to the dismay of corrupt governments and corporations across the planet, it’s ridiculous to believe that by arresting the supreme members of LulzSec that you have stopped us.”
The announcement was picked up by tech news sites like WebPro News[62] and ZDnet[63] with reserved skepticism towards its validity, speculating that FawkesSecurity could be a mere copycat group seeking to piggyback on the notoriety of Lulzsec. The doubts of ulterior motives were also driven by the revelation that the arrests in early March were directly linked to Lulzsec leader Sabu's cooperation with the federal investigators.
March 26th: Military Singles Dating Site Hack
In late March 2012, a group calling itself Lulzsec Reborn claimed it had hacked MilitarySingles.com, a U.S. military dating website, and released account information of over 170,937 subscribers via Pastebin.[64] The unauthorized release of personal data, which ranges from e-mail addressees and names to locations and IP addresses, was also announced through its Twitter account @LulzsecReborn:

"The website http://www.militarysingles.com/ was recently closed day ago or so, so we dumped email db. There are emails such as @us.army.mil; @carney.navy.mil; @greatlakes.cnet.navy.mil; @microsoft.com; etc."
MilitarySingles.com, an online dating service website for single soldiers who want to meet peer members of the service or people with shared interests in military lifestyle, is run by a firm called eSingles Inc. According to various news reports, the group gained access to the internal database on March 25th and as a proof, it tweeted a link to a defaced webpage hosted under MilitarySingles.com, which credited the breach to an anonymous hacker known as "lalalalala." The company has yet to comment publicly on the breach.

June 3rd: Lulzsec Revenge Announced
On June 3rd, 2012, YouTube channel Cocksec uploaded a video communique titled "Lulzsec: ALL YOUR BASE ARE BELONG TO US," vowing to release 3 terabytes worth of sensitive information it allegedly obtained from various governmental servers. Created in the style of Star Wars opening parody, the video also provides a short list of targeted websites includes the U.S. State Department (state.gov), U.S. Immigration and Customs Enforcement (ic.fbi.gov) and Defense Intelligence Agency (dia.mil), as well as Syrian government servers and Colombian prison servers among others that were unmentioned.
This time you won't see us coming.You'll just eat cock. That's all you will get. We're the ghosts you've created.
The video announcement of Lulzsec's comeback was immediately met by skeptical comments questioning its authenticity, perhaps due to an unsuccessful attempt at reviving the campaign in March, but the video continued to gain attention after it was endorsed by prominent Anonymous affiliates like @AnonymousIRC, @SgtSecondary and @WikiLeaks, according to the Daily Dot.[65] As of 2:35pm (ET) on June 5th, the video accrued more than 112,000 views on YouTube.
Trial
June 21st: First Arrest
On June 21st, 2011, 19-year-old Ryan Cleary was arrested by UK police for allegedly attempting to take down a police website. According to PCWorld[6], his arrest was related to an investigation into LulzSec's attacks:
The Metropolitan Police Central e-Crime Unit (PCeU) said the teenager was detained following an investigation into network intrusions and distributed denial-of-service (DDOS) attacks against "a number of international business and intelligence agencies by what is believed to be the same hacking group."
LulzSec denied that Ryan was a part of the hacker group, and only had minor involvement hosting one of thier irc chatrooms on his server.
Ryan Cleary is not part of LulzSec; we house one of our many legitimate chatrooms on his IRC server, but that's it. youtube.com/watch?v=Jf7iBS…
— The Lulz Boat (@LulzSec) June 21, 2011
July 26th: Lulzsec Spokesperson "Topiary" Arrested
On July 27th, the British Metropolitan Police arrested a 19-year-old Scottish resident in the Shelter Islands on charges related to cybercrime, hacking and network intrusions. Known by his online handle Topiary, the teenager is suspected to be the spokesperson of Lulzsec and account holder of the group's Twitter account. In addition, another teenage suspect was detained and questioned by the police in Lincolnshire, England, though no arrest has been made.

Since the arrest in the morning, there has been no Twitter update posted by @Lulzsec (as of 3pm EST) and all Topiary's personal tweets via @Atopiary have been removed, with the exception of one tweet originally posted on July 21st:
You cannot arrest an idea.
— Topiary (@atopiary) July 22, 2011
Topiary Unmasked
On Monday August 1st, 2011, it was revealed that the man accused of being LulzSec member Topiary was Jake Davis, an 18-year-old from the Shetland Islands. According to The Next Web[16], a photo was taken of him outside of his first court apperance wearing a blue shirt and black sunglasses:

The suspected LulzSec member is accused of coordinating Anonymous and LulzSec attacks from his home in Yell, on the Shetland Islands. His laptop was examined and it reportedly showed that he wrote a fake article claiming that Rupert Murdoch was dead, and such an article appeared on the Sun’s website recently when its own website was hacked. The hearing today also revealed that Davis’ computer had 750,000 people’s personal details, including private log-in information.
September 2011 Arrests
Two men reportedly sharing the handle "Kayla" were arrested by Scotland Yard on September 2nd, 2011.[17] The two men, ages 20 and 24, were accused of taking part in the HBGary Federal attack earlier this year. The attack was spurred after the CEO, Aaron Barr, bragged about infiltrating Anonymous via faux Facebook profiles.[18] Anonymous retaliated by hacking into Barr's personal email as well as HBGary servers, leaking thousands of confidential emails.

On September 22nd, 2011, 23 year old Cody Kretsinger, a college student in Phoenix, was apprehended by the FBI for allegedly participating in the Sony hack.[19][20] Known as "recursion," he was charged with conspiracy and the unauthorized impairment of a protected computer.[21] On October 17, 2011, Kretsinger entered not guilty pleas on both counts and is facing 15 years in prison.[23]
The same day, the FBI also arrested two men in California: Christopher Doyon, known as "PLF," "Commander Adama" or "Commander X," and Joshua Covelli, known as "Absolem" or "Toxic."[22] They were charged with conspiracy to damage a protected computer and two counts of aiding and abetting that damage. The FBI also issued search warrants for suspected Anonymous members in New Jersey, Minnesota, and Montana.
August 28th: Lulzsec Member Arrested
On August 22nd, 2012, The FBI issued a federal grand jury indictment charging a 20-year-old Arizona resident Raynaldo Rivera on counts of conspiracy and unauthorized impairment of a protected computer, specifically in regard to the breach of Sony's internal database which took place between late May to early June 2011. Nearly a week later on August 28th, the FBI unsealed the indictment papers shortly after it was reported in the news media[67][68] and the tech blogosphere[66] that Rivera, also known by his online handles "neuron" and "royal," had turned himself into police custody.
According to the indictment, Rivera is accused of conspiring with another suspect Cody Kretsinger, whom he went to school with at the University of Advanced Technology, to breach and obtain confidential data from Sony Pictures' computers, as well as publishing the stolen personal information on the Lulzsec website and its Twitter account. In addition, Rivera is also accused of using a proxy server in an attempt to hide his IP address and avoid detection from the authorities. If convicted on all charges, Rivera faces a statutory maximum sentence of 15 years in prison.
April 19th: Recursion's Sentencing
On April 18th, 2013, the U.S. District Court in Los Angeles sentenced Cody Andrew Kretsinger (a.k.a Recursion) to one year in federal prison and another year of home detention after his release, in addition to restitution of $605,663 in damage and 1,000 hours of community service. In April 2012, Kretsinger pleaded guilty to charges of conspiracy and unauthorized impairment of a protected computer during Lulzsec's major cyberattack against numerous databases of Sony database between May and June 2011.


May 16th: Sentencing in the UK
On May 16th, 2013, Ryan Ackroyd, Jake Davis, Ryan Cleary and Mustafa Al-Bassam were all sentenced at the conclusion of a two-day hearing at the Southwark Crown Court in London. Ackroyd, Davis and Cleary were each given prison terms of 30 months, 24 months and 32 months respectively, each required to serve at least half of the given time.[69] Al-Bassam was given 20 months of suspension and 300 hours of community service since he was only 16 when the hacking took place.[70] Following the sentence, Davis told the BBC (shown below) that he regretted 95% of his internet experience.[71] He said he learned that the internet had no empathy for others, causing him to become a very cynical person. As of May 16th, Raynaldo Rivera still had to be sentenced in the U.S. District Court in Los Angeles.
Search Interest
External References
[2] Gawker – Hackers Take Down CIA Website / 6/15/2011
[3] VentureBeat – Hit the deck: LulzSec and Anonymous start trading blows
[4] Linear Fix – Why LulzSec Hacks: A Timeline of Major Hacks
[5] Pastebin – Operation Anti-Security
[6] PCWorld – UK police arrest teen from Lulz Security for DDOS attack
[7] Wikipedia – Tupac Shakur
[8] cnet News – PBS, hacked, says Tupac is still alive
[11] Pastebin – 50 Days of Lulz
[12] Pastebin – Followers Graph
[14] Gizmodo – LulzSec Hacks The Times with Brutal Murdoch Death Notice
[15] LulzSecExposed – Topiary Doxed
[16] The Next Web – LulzSec’s ‘Topiary’ had 750,000 people’s personal details, prosecutors claim
[17] Fox News – Scotland Yard Arrests LulzSec Hacker 'Kayla'
[18] Computer World UK – UK Anonymous and LulzSec arrests linked to HBGary breach
[19] Fox News – EXCLUSIVE: FBI Arrests Suspected LulzSec and Anonymous Hackers
[20] NakedSecurity – Homeless hacker arrested by FBI in LulzSec/Anonymous investigation
[21] FBI – Member of Hacking Group LulzSec Arrested for June 2011 Intrusion of Sony Pictures Computer Systems
[22] AnonymousDown – Indictment of Anonymous / Lulzsec Members
[23] Reuters – Accused LulzSec hacker pleads not guilty in Sony breach
[24] Owni – LulzSec Arrests: A Warning to Dissidents?
[25] HideMyAss – LulzSec Fiasco
[26] AirVPN – Important notice about security
[27] Privacy International – Enjoy Internet Freedom and Anonymity (Terms and Conditions Apply)
[28] Guardian – LulzSec IRC leak: the full record
[29] Examiner – Anonymous punishes Florida Family Association for promoting bigotry, hatred
[30] Examiner – Anonymous hacktivists strike Portugal after police brutality
[31] Dark Reading – Resurgent LulzSec Attacks Government Sites In Portugal
[32] Pastebin – #FloridaFamilyJUSTtheBeginning
[33] YouTube – TheDigitalfolklore's channel
[34] BoingBoing – Anon releases FBI conference call
[35] Talking Points Memo – FBI Investigating ‘Illegally Obtained’ Conference Call On Anonymous Probe
[36] The Guardian – Anonymous's release of Met and FBI call puts hacker group back centre stage
[37] BBC – Anonymous gain access to FBI and Scotland Yard hacking call
[38] New York Times – F.B.I. Admits Hacker Group’s Eavesdropping
[39] FBI.gov – Six Hackers in the United States and Abroad Charged for Crimes Affecting Over One Million Victims
[40] Wired – LulzSec Leader Was Snitch Who Helped Snag Fellow Hackers
[41] Criminal Docket for Case # 2:11-cr-00766-URC filed August 10th, 2011
[42] @anonymouSabu – Tweet from August 17th, 2011
[43] United States of America v. Hector Xavier Monsegur
[44] … – New developments
[45] Jester's Court – If I am Wrong… I’ll say I’m Wrong. Here’s my apology.
[46] Gizmodo – LulzSec Leader Betrays All of Anonymous
[47] Gawker – Anonymous Snitch Tried, and Failed, to Pass Himself Off As an FBI Agent Last Month
[48] … – Uncovered: The Sabu Connection
[49] Huffington Post – Hector Xavier Monsegur, 4 Other Reported LulzSec Hackers Arrested By FBI
[50] Reuters – U.S. charges members of hacking group Anonymous
[51] TIME – Alleged LulzSec Hackers Arrested as Leader Turns Snitch
[52] Forbes – Top LulzSec Hacker Sabu Identified, Reportedly Worked As Government Informant
[53] Politico – FBI busts Anonymous, LulzSec ring
[54] Scribd – Hammond, Jeremy Complaint
[55] The Guardian – LulzSec leader Sabu was working for us, says FBI
[56] Fox News – EXCLUSIVE: Infamous international hacking group LulzSec brought down by own leader
[57] New York Times – LulzSec Hacking Suspects Are Arrested
[58] CNN Money – Anonymous in disarray after major crackdown snares leaders
[59] the Wall Street Journal – U.S. Swoops Down on Alleged Computer Hackers
[60] BBC News – 'Lulzsec hackers' arrested in international swoop
[61] Twitter – @anonymouSabu
[62] WebProNews – Lulzsec May Be Getting the Band Back Together
[63] ZDNet – Anonymous Lulzsec Returns on April Fool's Day?
[64] Pastebin – #Lulzsec Reborn
[65] Daily Dot – LulzSec returns with an alleged 3 terabytes of data
[66] Gizmodo – LulzSec’s Topiary Talks About Life After Hacking, Says He Feels More Fulfilled Without Internet
[67] Reuters – Second accused LulzSec hacker arrested in Sony Pictures breach
[68] Los Angeles Times – Second LulzSec member indicted, allegedly for attacks on Sony Pictures
[69] Cnet – LulzSec case in U.K. brings sentences for 4 men
[70] Wired – LulzSec Hackers Sentenced to Prison by London Court
[71] BBC – Former Lulzsec hacker Jake Davis on his motivations




















Comments ( 176 )
It’s interesting. I would like to see more this group can hack.
Right now I’m like: 1+ wait
+1 work, this has happened and I do think they have potential, so +1 wait.
lol! these guys are great!
the jester posted this http://lulzsecexposed.blogspot.com/
Well this is disappointing somewhat to me. I was hoping they did hack Sega. Sega isn't that cool imo.
Wow… These guys are powerful. Reminds me of anonymous.
+1 confirm! These guys have made their name known.
Not really a meme. Just an organisation of Hackers.their popularity is rising, but i dont really class things like this as a meme. Still, quite notable.
+1 confirm now, they seem like lovely chaps.
1+ enough waiting.
1+ Confirm
Wow i though they were that same as the Anons and part of 4chan…i guess not…if 4chan is the Anons hang out i wonder what these guy's hangout is.
@Mulac The Rich Hobo
That's kinda why this is classified as an event, not a meme…
@Ashley Rodriguez -- This ought to be interesting. While Anonymous has greater numbers, as well as greater durability (because of it's nebulousness), LulzSec has tighter organization and greater capability. While Anonymous has to rely on brute-force methods and DDOS attacks, LulzSec can pull together more sophisticated hacks because of its greater cohesion and skill. LulzSec does, however, have a leadership structure, and if Anonymous can get hold of their contact information, they can hand it over to the police and take the whole group down. This will be fun to watch.
could you imagine 4chan vs LulzSec it would be a very close battle
The fun seems to have just about started!
+1 wait
Although this vs off would be interesting :( can't we just not do it? Lots of us like both sites
+1 wait…
there growing massively, but im not sure if theyre at meme status yet
They attacked Minecraft?
Death to LULZSEC!
Minecraft…Y U ATTACK DAT GAME?
You must die! Lulzsec!
+1 event
I bet they did it for the lulz, whos with me on that?
I hope these two just destroy each other.
Dear god…. I just realized something. First conflicts between Noelisme and Anon…. then Lulzsec breaking from 4chan and DDOSing it's parent website…. anti-internet freedom legislation from Congress and attacks by Lulzsec on the CIA bringing the federal government into the mix … holy cow, World War 3 is going to take place on the internet. This could be epic guys… let's just hope they don't accidently the internet.
So, any predictions on how this war is going to fare? Alliances? Betrayals?
Really, it's more of a World Wide Web War.
It seems to be Hacktivists vs. Governments and Economical Superpowers. Anon takes down the Chamber of Commerce website because of the new PROTECTIP Bill, Lulzsec takes down the CIA website. Jesus Christ, if Anonymous and Lulzsec were to settle their differences, we could have complete and total control over the Internet and Television.
I love hackers
https://www.youtube.com/watch?v=-hKKgPYYt7Y&feature=related
It sounds like Anonymous is taking internet freedom seriously, whereas LulzSec are just a pack of annoying trolls.
Cool
@megafest7 agreed.
I could be wrong, but I was watching the news amd it said he got arrested, it could be a different guy tho..
@Mettie7 Eeeyup! I read it too
Messing with 4chan = DOOM
Looks like British Int. claims to have arrested someone. Always funny when you see people like this pop into "IRL."
Nothing against those who are actually trying to do good work, but it seems like a majority of these Lulzsec and Anonymous folks are just people who never got over their rebellious teen stage and are now trying to rebel against "the man" from their parent's basements.
@Nevar00
Yeah, i guess those Colonial buggers who sat around in meetinghouses talking about dumping tea shipments just because the tea was a little bit too pricey never got over THEIR rebellious phases either.
Srsly, go read some Neil Stephenson.
@FlintTD
You're comparing the Founding Fathers to a group who hacked a website with Nyan Cat and pulled down some online gaming servers, all behind the anonymity of the internet.
@Nevar00 BULLSHIT AD HOMINEM ARGUMENT IS BULLSHIT
Seriously. What fucking difference does that make. One defaces websites to make its point, one dumps tea into the harbor.
I support anonymous's cause. I think lulzsec are jerks.
They seem like a bunch of arrogant and cocky internet trolls defacing government websites, hacking PBS, and shutting down game servers for the hell of it while attempted to come off as White Knights, and I can't see most of them still being around in 6 months. But whatever.
I'm neutral towards these guys, but I think I should keep an eye on them…
So this is the scum that swamped online gaming!
DEATH TO LULZSEC!!!
Find them. Court them. Send them to Alcatraz for 20 years minimum.
Alcatraz isnt in use, or youre an ignorant, or youre a kid.
It's like there's new categories of people in their anonymity.
LOL, he has the same surname as me
FREEDOM!
Well… I miss that…
I've already bought a dog and cleaned my curtains for the incoming hacker wars. I suggest everyone else does the same.
What LulzSec want? Become the most famous hacker of the world? He hacked brazillians webpages. (nice, i live in brazil and i watched that today).
I don't know what he want… but he got a PRICELESS AVATAR FACE
This is yet another thing contributing to a possible future sh*tstorm, I just realized…
If Anon and LulzSecurity had the same goals along the lines of internet freedom and freedom of information… I'd be scared if i was against them right about now.
While I am generally impressed by Anonymous and support their causes, I must point out that LulzSec has no overarching concept of justice, and they're simply a bunch of hacker scum looking for trouble. iamdisappoint.jpg
Bloom County strips like this one came to mind…

I wish I could find one of the comics where he dressed as a pirate…
on thier twitter they said
"Got some nice things for Friday. Hopefully Payload #1 of many to come!"
http://twitter.com/#!/LulzSec
Are they doing anything about this whole 'Censor the Internet' stuff? They should stop doing things for the lulz and actually focus on important things. I'm disappoint that Anonymous joined them :L
They just talked about this on The Daily Show, the hackings, not his arrest
They were just talking about this on The Daily Show.
I have a bad feeling about the future of the gaming industry, and any online entertainment as a whole. They did a massive DDoS wipe on the League of Legends servers. Same with EVE online, TF2, Minecraft. Everquest servers weren't so lucky (the server got shut down entirely, Sony had to take down the site for a whole month to fix it).
Whoever these men are they are good at what they do. I don't want to mess with them but at the same time I wish them ill. Nothing kills the mood like crashing the server millions of people worldwide log into. Thats deep.
I can't be the only one that suspects curse/mmo-champ was taken down by Lulzsec? It's been a few days…that's not average maintanence.
I agree with Emew, it's sort of odd how long all their sites have been down.
Also, +1 confirm.
Not sure if this is old news, but Lulzsec was prominently featured in an article in the latest Time magazine.
It's too bad they can't work to take down child molesters and animal abusers (and bigger fish as well), sort of in the same way 4chan has done on a few occasions. Releasing personal information of cops and how informants are handled? How the fuck does that help anything?
http://english.aljazeera.net/news/americas/2011/06/20116242002307617.html
Arizona, Lulzsec hacked the border patrol.
@Sweatie Killer

Lulzsec+Anonymous=FULL OF WIN
This should have a 5 star featured badge because it's been featured at least 5 times.
Daily Show talked about these guys yesterday.
What are they doing bringing down gaming servers? What point could they possibly be making like that?
These guys are amateurs. Arizona Dept of Safety? LOL
There won't b e many Lulz when the orange jumpsuit goes on (or off, in the prison shower).
With the power of LulzSec combined with the sheer numbers of Anonymous, they are unstoppable. All is lost.
Lulzsec, anonymous and all other hacker groups are under threat at the moment so it seems they're banding together to defend themselves. I think the government's going to win this personally.
Well, that was unexpected.
I'm sure we'll see them again, though. Or maybe just some wannabees…
Haha retiring? More like running scared and hiding from the cyberpolice backtracing them :3
LULZ SEC,
Y U NO KEEP SAILING THE LULZ BOAT?
Thank God, this was getting out of hand.
˙ǝzınb ǝsǝɥʇ buıʎoظuǝ sɐʍ ı ¡uɹɐp
I don't get what's up with taking down security related things. We need security and government.
We don't need government hiding stuff when they say that the public deserves to know the truth.
NNNNOOOOOOOOOOOOOOOOOOO THEY CAN'T RETIRE`!!122!!!@
@RussianFedora: Isn't it obvious? One of their buddies got arrested and now they're abandoning ship as fast as they can.
Aww, LulzSec, you'll be missed. :<
@NotADog:
Possibly.
darn it! I wanted them to hack the pentagon next!
Never heard of them.
@lotlat Well,seeing as to how if someone were to try to hack into the Pentagon it would be seen to the government as an act of war,not full blown war,obviously but you sure as hell won't be alive by the end of the week.
@notAdog ha! True…I think they have (had) a great power, but they made some huge mistakes…
How has this not been confirmed yet?
Not retired, but trolling.
The end of and era :'(
lulzsec is fail
Many threats from the cyber police, eh? I knew this would end soon.
Thank god they handed things over to Anonymous. Maybe they'll use the power for good, and not for lulz..
And that is why you should stay anonymous doing this things. Why glorify a name if you are only going to get caught?
I do hate that they hacked Sony…..why not hack a company that really wants to suck the money out of you, like Microsoft?
They forgot their seven proxies. Those idiots.
Hahahaha so Lulzsec acts like tough shit then once a REAL hacker comes and reveals them they high-tail out ASAP and call it 'retiring.' Priceless. Good riddance Lulzsec, I always saw them as arrogant douches.
And with LulzSec dying, spamtrolls spam spam on entries about them.
These guys are pretty impressive…
But i'm a little peeved at them because they caused the takedown of the minecraft wiki+forums.
I am in AWE!
Good, now I might finally stop hearing about them and their stupid, unfunny, hypocritical horseshit.
Good riddance.
Lulzsec was being targetted by anothe rhack group the A-TEAM themselfs http://blog.alexanderhiggins.com/LulzSec-And-Anonymous-Hacker-Identities.html
Im guessing he will probably make a breif return in about a year or so.
Why does LulzSec retire? Can't they face the consequences of their acts like men?
Cowards…
@People who think they will be retiring
They won't. Hackers do not retire.
Can somebody tell me what this is actually?
I hope lulzsec comes back. IF they do come back, they should start with a grand entrance: The hacking of every Australian school proxy. Set all passwords to poptart cat! lulz…..
then again… we are talking lulzsec… so they probably are still out there… hacking somewhere… ddosing someone…
lol they realized they shot themselves in the foot when they hacked into things better and more heartless hackers enjoy (minecraft, games) and are trying to disappear by becoming some new group, as if by changing their name they're not the ones who did it. So for those hackers who want to get back at them for taking away your games, continue on finding them, outting them, and hack them. Then post it for us all to lulz at the irony. Run scared little Lulzsec kids. You wont be forgiven.
@ M_M_
The cool thing is that, as far as I know at least, hacking people like them who have hacked government websites is legally okay!
Hunt down lulzsec members through the internet, and change their computers power intake settings by getting control of their computer. Hardware melts, no more hacking :D
The Department of Homeland Security will knock on your door if you steal a phone, and these guys were hitting websites run by governments. What did they think would happen? Sure, those websites were meaningless to the people running them, but it's still borderline cyber terrorism. Have fun with that gents.
hate hackers. using their knowledge of computers for cyber terrorism? for laughs?? some men on the internet are just twisted, thats for sure.
This was very confusing and my lack of understanding limited my capacity to give a fukc.
LulzSec, you were an impressive group of hackers. xD
(0_ಠ)-Y
Lame attempt at making an emoticon.
… This isn't even a meme.
@Idreamofcheese
No. No it's not. And Thats why its labelled "Event". Not meme. Learn to read man.
http://www.thesun.co.uk/sol/homepage/ now redirects to the Lulzsec twitter account. Well played.
UNRETIRED, BITCH!
Not retired, just Zalgoing
They hacked News of The World. LOL.
fucking bullies. X-Factor contestant personal info for scams, etc. Way to stick it to the man. Not against hacking groups, but stick to the people who deserve it.
I like how Lulzsec is usually un-serious and funny.
god , i love those guys
Come on Lulzsec. Why did you knock down Sony? And take my credit card data! Why don't you own Microsoft, and Xbox live instead? That's alot worse than Sony.
So are we placing bets for how long it takes before a bunch of them get arrested and Lulzsec "retires" again?
By messing with American corporations, you're messing with the US government. By messing with the US government you've messed with the US department of defense. We spend 690 Billion dollars a year on our military (about 2x times more than the entire world combined), which includes cyber warriors, the amount of fucked they are is tremendous. Be funny if the CIA hacks their twitter and uploads a picture of them waterboarding their leader while laughing their asses off. God Bless America!!
I've had suspicions that one of them was paid to help start this stuff. The latter attacks seem to derive too much from the purpose of the main attacks and seem to be more pranks than statements.
Me and my dad were watching the news when this story came up, i instantly knew who the perpetrators were before the story was even explained. LulzSec FTW
"TheSun.co.uk now redirects to our twitter feed." ~ LulzSec

I can somehow imagine how they came up with that idea:
@Terrortoast:
Cant tell if trolling
¦¬|
Or just nationalist
@TheFonz You're a complete moron. Point blank.
I'm glad they took down Sony.
Probably because I"m the only one in my town or school that play Nintendo.
And I say just because it has big graphics doesn't make the gameplay better.
It only makes people who play Sony dumb and stuff.
Also graphics ain't everything.
Because ten year's later you can't feel nostic or how ever you say.
SO If their ever back they should take Sony down completely.
Lulz for the win!
Hey guys, I think you forgot an important one.
The tenth of June, the entire phone-network in Norway went down.
People couldn't call, send messages, or anything.
It stayed like that for 18 hours.
According to "Vi Menn", a Norwegian magazine, (albeit a bit sketchy), Vi Menn had contacted a Norwegian man who claimed that Anonymous attacked their servers with a DDoS attack, using a bot-net, with help from Lulzsec.
He also promised another attack.
Short version, Norwegian: http://www.klikk.no/produkthjemmesider/vimenn/reportasje/article691615.ece
I like their goals, but I don't agree with how they are going about reaching them.
I feel that there should be SOME internet censorship, particularly for illegal things (terrorism, pirating, stolen goods, etc.), but things that don't negatively affect anyone and don't cause problems shouldn't be censored.
@Check Engine Light – I guess you were right. And I do actually understand why they did it. I think it's good that they brought attention to internet security, and how easy it is to hack websites and get information off it. Although, I do not agree 100% with their methods.
TROLLED TROLL
they fought the law and the law won, or at the very least I hope it does so that the reference is complete.
I would never they are an impressive group of hackers. Just about anyone with computer knowledge can do so. Im pretty glad they are starting to fail because im tired of people talking about it. At first it was funny but at this point it has been dragged on for to long.
@OccasionallyNotStupid
Hey if it doesn't we can go I fought the law and I won to twist it into a Dead Kennedys reference instead.
Oh Lulzsec, I miss you so <3
I hope you guys make a comeback soon!
They arrested a homeless guy.
I can't even.
I'm serious, I can't even.
they're just getting desperate in finding members of Lulzsec now.
The same day, the FBI also arrested an homeless man they claim is a member of Anonymous
Wat.
The FBI must of gotten trolled.
Well, it looks like LulzSec…
puts on sunglasses
Needs to up their security.
YYYYYYEEEEEEEAAAAAAAHHHHHHHH!!!!!!
or maybe this :
"I'm gonna find them. One way, or another."
I could give two turds about their "hacktivism." I just think their logo is friggin' adorable.
Long live LulzSec.
Who the hell arrests a homeless man? If he's been Homeless before April 2011, like hell he was involved with LulzSec?
What the fuck F.B.I?
Hilarious the __sec group think they are untraceable. That somehow their connection is magic while everyone else's are physical. If you get your internet from a company, lol you're going to be found. Just because it isn't done within a week doesn't mean it wont happen.
Can't get everybody….
cool story bro
Sabu: He's not hardcore.
They started out as concerned individuals trying to make up for the inevitable short-comings of the law.
They allowed pride to corrupt their ideals.
They eventually reached a point of hubris where they were believing that they were judge, jury and executioner. They were playing god, so to speak.
Frankly, in spite of their noble start, it's good they got arrested. Their arrogance got the better of them and they went from vigilantes going after the corrupt to bullies going after anyone they didn't like personally.
Bless you
what if they hacked us? they better not take my email!
You dont seem to understand the concept of these groups… They dont give a fuck about us normal civilians…
so the circle of life begins anew; lulzsec reborn is lthe phoenix that rises from its ashes and prepares to scorch the ground
so poetic…nah these motha fuckers are gonna quit so fast before you can even say what
Theyre thumbing down, yeah, like if we care
Wtf is this shit
kings and queens, governments, dictatorships, corporations, lobby groups, gangs, organized crime rings, hacking groups
absolute power corrupts absolutely
Am I the only one who thinks that the story of LulzSec/Anonymous would be an interesting documentary?
Jesus H. Christ… didn't any of these "hackers" know how to use TOR ?!
Hacker 101:
First rule: hide your tracks.
Internet freedom does not mean the freedom to invade other people's servers or stealing people's privacy. Privacy is one right that all internet freedom advocates should be in favor of, and that is a right that many of these so-called "hacktivists" do not have any respect for-- except for when they are getting busted by the cops.
I'm glad to see these jerks get what was coming to them. There are plenty of aspects of internet regulation that I think we should have a healthy debate over (I personally think that regulation should be as minimal as possible), however a person's private information like credit card numbers, banking information, SSNs, passwords, etc. should not be up for debate. Just because you have a computer does not give you the right to steal that information from people.
You got thumbed down by hacktivists and followers, and ill probably be too
well the internet pretty much like computers are tools, and always using a tool wrong will backfire
Frontpage of Encyclopedia Dramatica, June 1st
3 more Reddit pedos put where they belong. Watch out for that dropped soap guys!
You got thumbed down by hacktivists and followers, and ill probably be too
Theyre thumbing down, yeah, like if we care
Bless you
Alcatraz isnt in use, or youre an ignorant, or youre a kid.
And ceiling cat watched the tyrant governments as they kept secrets and did bad stuff.
He was not plzd.
And then ceiling cat sent down a band of angels, known by the ancients as Lulzsec, to save the worlds.
They got secrets and shared them among the boys and girls of the internets, and defeated the evil governments.
It was gud.
You dont seem to understand the concept of these groups… They dont give a fuck about us normal civilians…
Hackz Rules
1. Never Tell Your Parents
2. NEVER TELL YOUR PARENTS!!!!!!
Hacked many companies, and even hacked the governmental servers
Then they got arrested
That icon.
i recommend you talk to emmy for any hack operation and database extrat needed. his contact on whatsapp – +16625918530 or email-emmyhackengine@gmail.com
It was through these guys that I first learned about bitcoin, since they were asking for bitcoin donations. These guys represent an era of hacking.
Sorry, but you must activate your account to post a comment.