Hacktivism / Internet Vigilantism
Submission 37,425
Part of a series on The Internet. [View Related Entries]
Hacktivism / Internet Vigilantism
Part of a series on The Internet. [View Related Entries]
[View Related Sub-entries]
This submission is currently being researched & evaluated!
You can help confirm this entry by contributing facts, media, and other evidence of notability and mutation.

| Navigation |
| About • History • Related Memes • Search Interest • External References • Recent Images • Recent Videos |
About
Hacktivism refers to people, notably Anonymous, acting outside of the criminal justice system to carry out vigilante missions through the subversive use of computers or the Internet.[5] The alternate term Internet Vigilantism is often used as a synonym though the terms have nuanced differences.[4]
History
Hacktivism is a portmanteau of "hack and "activism" first coined in 1996 by the user Omega, a member of the legendary hacker collective Cult of the Dead Cow.[14] The most notable incidents in the timeline of hacktivism are the founding of Wikileaks in December of 2006,[17] Project Chanology in January of 2008,[15] NSA Surveillance Scandal in June of 2013,[16] and the 2016 United States Presidential Election Hacks.[18]

Anonymous
Anonymous is an ad-hoc group of Internet users who are often associated with various hacktivist operations, including protests against Internet censorship, Scientology and government corruption. Users of the anonymous image board 4chan, launched in late 2003, began using the term “Anonymous” when referring to themselves as a collective. User registration is not required on the site and users who do not identify themselves are given the label “Anonymous.” In 2004, a 4chan administration manipulated the site to force every user to be displayed as “Anonymous,” which perpetuated the notion that users of the site was part of an anonymous group.

Piracy
Piracy on the Internet is a form of copyright infringement in which the pirate uses copyrighted works while infringing exclusive rights granted to the copyright holder without the owner's permission.[25] Online piracy of content is viewed as a form of hacktivism done either in protest of the copyright or the copyright holder. Those who pirate in defiance of copyrights in general do so out of a belief in free shared information for all,[26] while those who pirate in defiance of the copyright holder do so on a case-by-case basis of how they view production/selling of the product.[27]

The Pirate Bay
The Pirate Bay (TPB) is a torrent hosting website where users can share files using the BitTorrent protocol. The site has often been criticized by companies in the entertainment media industry for facilitating Internet piracy and copyright infringement. The Swedish anti-copyright organization Piratbyrån (“The Pirate Bureau”) was established on August 1st, 2003, which aimed to support file sharing on the Internet in opposition to the Swedish Anti-Piracy Bureau. On September 15th, 2003, Piratbyrån members Gottfrid Svartholm and Fredrik Neij launched the torrent sharing site The Pirate Bay.[28]

Bitcoin
Bitcoin is a virtual, decentralized crypto-currency regulated by a peer-to-peer network that creates a time-stamped register yielding chains of valid transactions. Unlike other digital currency systems or credit payments, Bitcoins are treated like cash and transactions cannot be reversed. They are notorious for being near impossible to track and have even been banned by China.[29] Bitcoins have become well-known among hacktivists for enabling anonymity and protest of centralized government currencies.

Tor
Tor, an acronym for "The Onion Router," is "a group of volunteer-operated servers that allows people to improve their privacy and security on the Internet."[19] It protects the user's privacy by "bouncing your communications around a distributed network of relays run by volunteers around the world."[20] Tor is used by people wanting to escape Internet censorship by their government and for spreading information which would otherwise be deemed illegal.

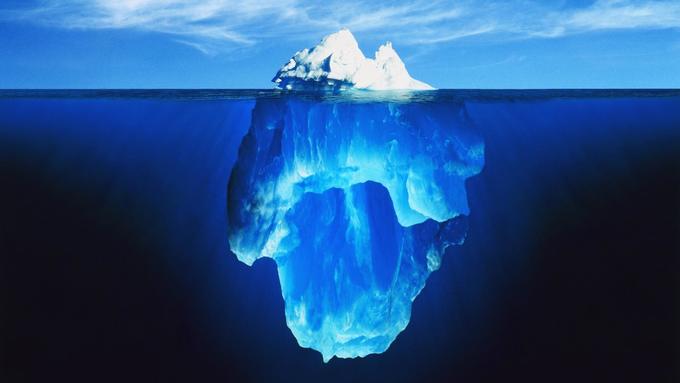
Deep Web
Deep Web, also known as “Deepnet,” the “Invisible Web,” the “Undernet” or the “hidden Web,” are parts of the Internet only accessible through browsers such as the Tor Browser that are not considered part of the “surface web,” or the portion of the World Wide Web that is indexed by conventional search engines. Many deep web sites are not indexed because they use dynamic databases that are devoid of hyperlinks and can only be found by performing an internal search query. The Deep Web has served as a hub for people to convey and sell illegal materials and advocate hacktivist views, the latter most notably demonstrated through The Hidden Wiki.
The Hidden Wiki
The Hidden Wiki is an onion link wiki page which has served as a makeshift homepage for users of Tor in addition to being a highly influential body of text among hacktivists.[22] Within, the wiki contains a page heavily discussing how The Matrix serves as the best metaphor for why organized evil and oppression are allowed to exist, as well as tactics for subverting the matrix. The site additionally provides various privacy tactics as well as its infamous list of sites for socializing, searching, darknet markets, security, media, info, doxed info, forged items, porn, drugs, weapons, and in older versions, hitmen for hire.
The Matrix
The Matrix is a notable movie, trilogy, and concept among hacktivists. The Matrix was originally the first installment in The Matrix Trilogy about a man named Neo who is good with computers and over the course of the film the iconic character Morpheus helps make him aware of the fact what he thinks is reality is in fact a simulation called the matrix. Morpheus offers Neo the equally iconic choice of taking either the red pill or the blue pill and upon Neo choosing the red pill, he begins his quest to exit the matrix, learn how to manipulate it, and over the next two films in The Matrix Trilogy, discover how to defeat the robots controlling it.[21]

Red Pill
Red Pill or Red Pilling is the metaphorical act of making oneself or another become aware of the unpleasant truth of reality. Originally introduced as a crucial plot device in the 1999 science fiction film The Matrix, the term has gained widespread usage online among hacktivists, conspirists, and political activists proselytizing their ideas. Conversely, the term “blue pill” is used to describe the act of choosing blissful ignorance over the brutal truth.

Julian Assange
Julian Assange is an Australian journalist and political activist best known as the founder and editor-in-chief of the international whistleblowing organization WikiLeaks. Since November 2010, Assange has been wanted by the British government for extradition to Sweden under an European Arrest Warrant relating to a sexual assault investigation and currently resides inside the Ecuadorian embassy in London as a political refugee.

WikiLeaks
WikiLeaks is an online publication most well-known for its disclosure of confidential and classified documents issued by public or private organizations and submitted by anonymous news sources, including the United States diplomatic cables leak in November 2010. The website was launched in December 2006 as a non-profit project of The Sunshine Press and the directorship of Julian Assange, an Australian journalist and hacker. The site claims to have been “founded by Chinese dissidents, journalists, mathematicians and start-up company technologists, from the US, Taiwan, Europe, Australia and South Africa.” Within the first year of launch, the site claimed a database of more than 1.2 million documents.

Kim Dotcom
Kim Dotcom born Kim Schmitz, is an Internet entrepreneur known for founding the online file storage website Megaupload. Kim founded the company Megaupload while living in Hong Kong on March 21st, 2005. The company consisted of several file hosting web services, including Megaupload.com, Megapix.com, Megavideo.com, Megalive.com, Megabox.com and Cum.com. Dotcom gained noteriety in January of 2012 when he was arrested by U.S. officials in New Zealand for violating copyright laws. Kim Dotcom denied any wrong-doing and the legality of his arrest and assets seizure has come under heavy scrutiny both from hacktivsts and from law professor Eric Goldman.[23] In response, the hacktivist group Anonymous retaliated by targeting and successfully taking down numerous U.S. government websites.[24]

Edward Snowden
Edward Snowden is an American system administrator and a former employee of Central Intelligence Agency (CIA) who worked as a contractor for the National Security Agency (NSA) before leaking highly classified information on the agency’s top-secret PRISM surveillance program to the British newspaper The Guardian in June 2013.

Related Memes
Net Neutrality
Net Neutrality is a network design principle and digital rights movement which advocates Internet service providers (ISPs) to treat all Internet traffic equally in order to maintain an “open Internet.” The principle is in opposition to a “closed Internet” in which providers restrict access to content, filter content or use “traffic shaping”[12] to degrade access to specific web services.

DDoS
DDoS (Distributed Denial of Service) is a method of cyberattack that usually involves temporarily blocking access to a website or server by flooding the bandwidth of a targeted network. The most common methods of DDoS include exploiting unprotected server networks, sending massive requests or opening multiple connections with the server. The first publicly available DDoS tools Trinoo and Tribe Flood Network were released in 1997 and 1998 respectively.[13] The first well-documented DDoS attack took place in August 1999, which targeted a single University of Minnesota computer and knocked the system offline for more than two days.

Doxing
Doxing, sometimes spelled as Doxxing, refers to the practice of investigating and revealing a target subject’s personally identifiable information, such as home address, workplace information and credit card numbers, without consent. The word is derived from “docs,” which is a shortened term for “documents.”

Hackers Gonna Hack
Hackers Gonna Hack is an expression derived from the meme Haters Gonna Hate that was first uttered by the former German Federal Minister of the Interior Thomas de Maizière[11] in response to interview questions about the security of the newly released electronic German identity card in September 2010.

Search Interest
External References
[1] Oh Internet – 8 Awesome Cases of Internet Vigilantism
[2] Canoe News – Man trolled the web for girls: cops
[3] Cracked – 8 Awesome Cases of Internet Vigilantism
[4] Wikipedia – Internet Vigilantism
[5] Wikipedia – Hacktivism
[6] We Are Legion Documentary – We Are Legion | The Story of the Hacktivists Official Website
[7] We Are Legion The Documentary – ABOUT THE FILM
[8] The Daily Dot – Why Alyssa Milano created a comic book tribute to Anonymous-
[9] Comic Vine – Archaia Entertainment Presents: Alyssa Milano’s ‘Hacktivist’
[10] Archaia – Hacktivist
[11] Wikipedia – Thomas de Maizière
[12] Wikipedia – Traffic shaping
[13] UniForum Chicago – What's new in DDoS
[14] Trend Micro – Hacktivism 101 A Brief History and Timeline of Notable Incidents
[15] Wired – War Breaks Out Between Hackers and Scientology -- There Can Be Only One
[16] NBC – Edward Snowden A Timeline
[17] Euronews – Julian Assange & Wikileaks Timeline of Events
[18] CNN – 2016 Presidential Campaign Hacking Fast Facts
[19] Tor Project – Tor Overview
[20] Tor Project – What is Tor Browser?
[21] IMDb – The Matrix Plot Summary
[22] The Hidden Wiki (accessible through Tor) – The Matrix
[23] TechDirt – Law Professor Megaupload Prosecution A 'Depressing Display Of Abuse Of Government Authority'
[24] BBC – Hackers retaliate over Megaupload website shutdown
[25] Wikipedia – Copyright infringement
[26] TorrentFreak – Pirate Bay’s Founding Group ‘Piratbyrån’ Disbands
[27] Gamerevolution – Sonic Mania's Denuvo DRM Has Been Cracked Eight Days After Launch
[28] The Pirate Bay – The Pirate Bay
[29] Crypto Coin News – ViaBTC CEO: China Will Ban Bitcoin Exchanges
Recent Videos 1 total
Recent Images 19 total
Share Pin













Comments ( 8 )
Sorry, but you must activate your account to post a comment.
Please check your email for your activation code.